A question that is raised frequently in conversations with our customers is Kaleido's support for "off-platform" keys. Our customers also love the simplicity of using Kaleido's Gateway APIs and the benefits it provides in terms of abstracting away the complexities around signing, nonce management, and transaction error handling.
HSMs (Hardware Security Modules) are a well-established industry standard that provide a secure way to store, manage, and use cryptographic keys for a specific set of cryptographic operations. So we set about building an interface that could talk to an HSM which can be provisioned in the customer's preferred cloud provider or deployed "on-prem", running in their own datacenter. The benefit to the customer is that they can use all the features of Kaleido and have the HSM sign transactions using keys that are stored in it.
The Cloud HSM Signer Services interface with the following HSM providers:
Microsoft Azure Key Vault is a FIPS 140-2 Level 2 validated HSM (hardware and firmware). Azure Key Vault provides the ability for users to import and/or generate keys that are stored in Key Vault. With Key Vault, Microsoft doesn’t see or extract the user's keys. Key usage can be monitored and audited.
AWS CloudHSM enables users to generate and use encryption keys on a FIPS 140-2 Level 3 validated hardware. CloudHSM protects keys with exclusive, single-tenant access to tamper-resistant HSM instances in the customer's own Amazon Virtual Private Cloud (VPC). AWS has no visibility or access to keys stored in AWS Cloud HSM.
Although Hashicorp Vault is not an HSM, it is a software that allows secure storage of encryption keys and policy-based access control to those keys. Vault is straightforward to set up "on-prem" by customers or can be set up in the cloud of their choice. We leveraged Vault's rich plugin-based architecture by developing an open-source plugin that is used to sign a transaction sent over secure HTTP to the vault using an account key of the curve secp256k1 that is stored in Vault. The plugin is designed to allow client access policies to be defined for user-level interactions (list key addresses, sign transactions) vs. administrator-level interactions (create/view/delete/list-keys, import/export-keys). This plugin has been tested with the Vault Open Source version 1.4.0.
We recommend customers consider the following aspects before choosing a Cloud HSM provider. Of course, a Kaleido environment can run multiple instances of Cloud HSM Signer service if customers wish to operate with signing keys distributed across one or more Cloud HSM providers.
The high-level steps involved in using the HSM Signer Wallet is as follows:
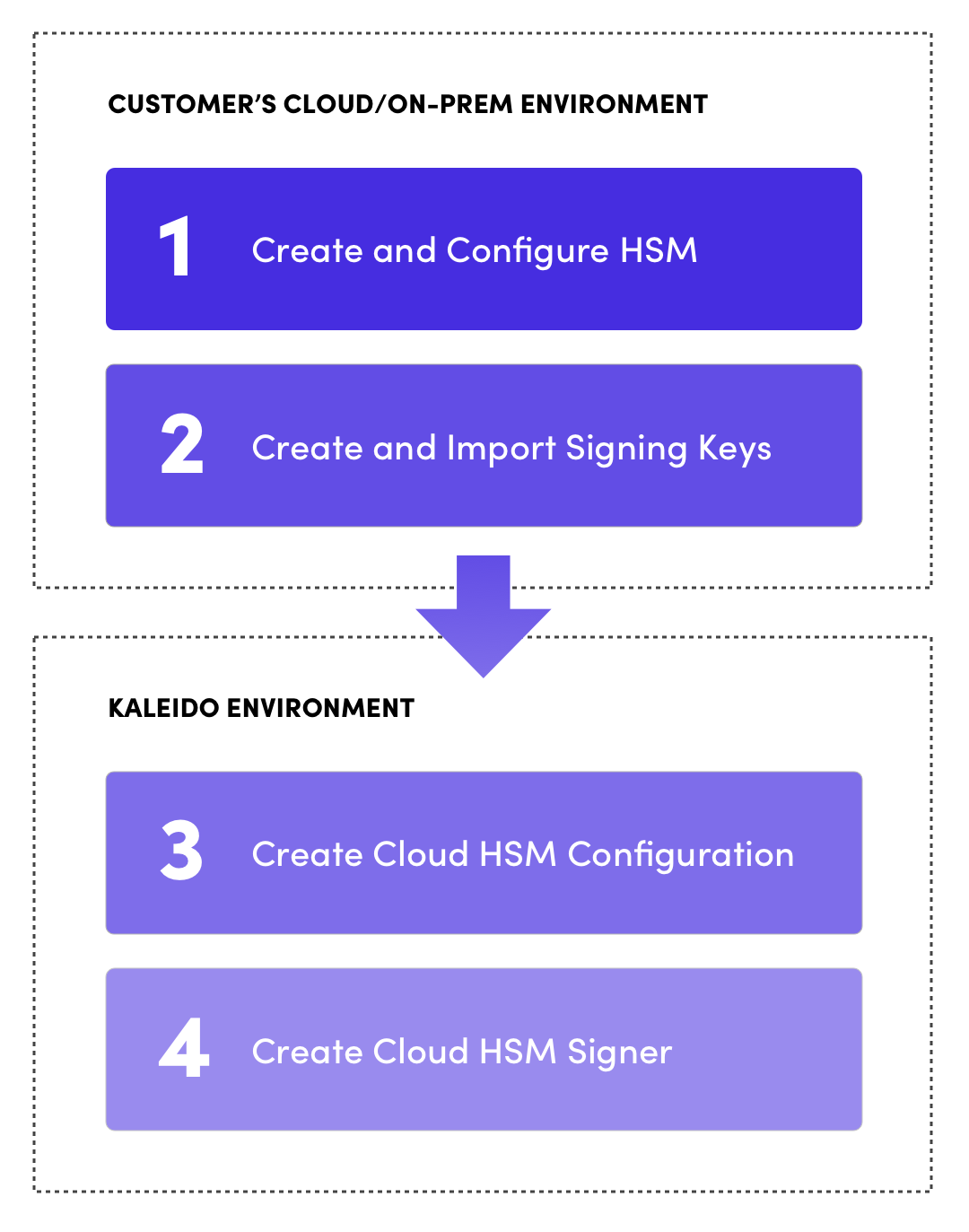
If you do not have a Cloud HSM backend configured and set up with keys that are to be used for signing transactions, check out the following links that provide details of how to set up and configure the backend of your choice.
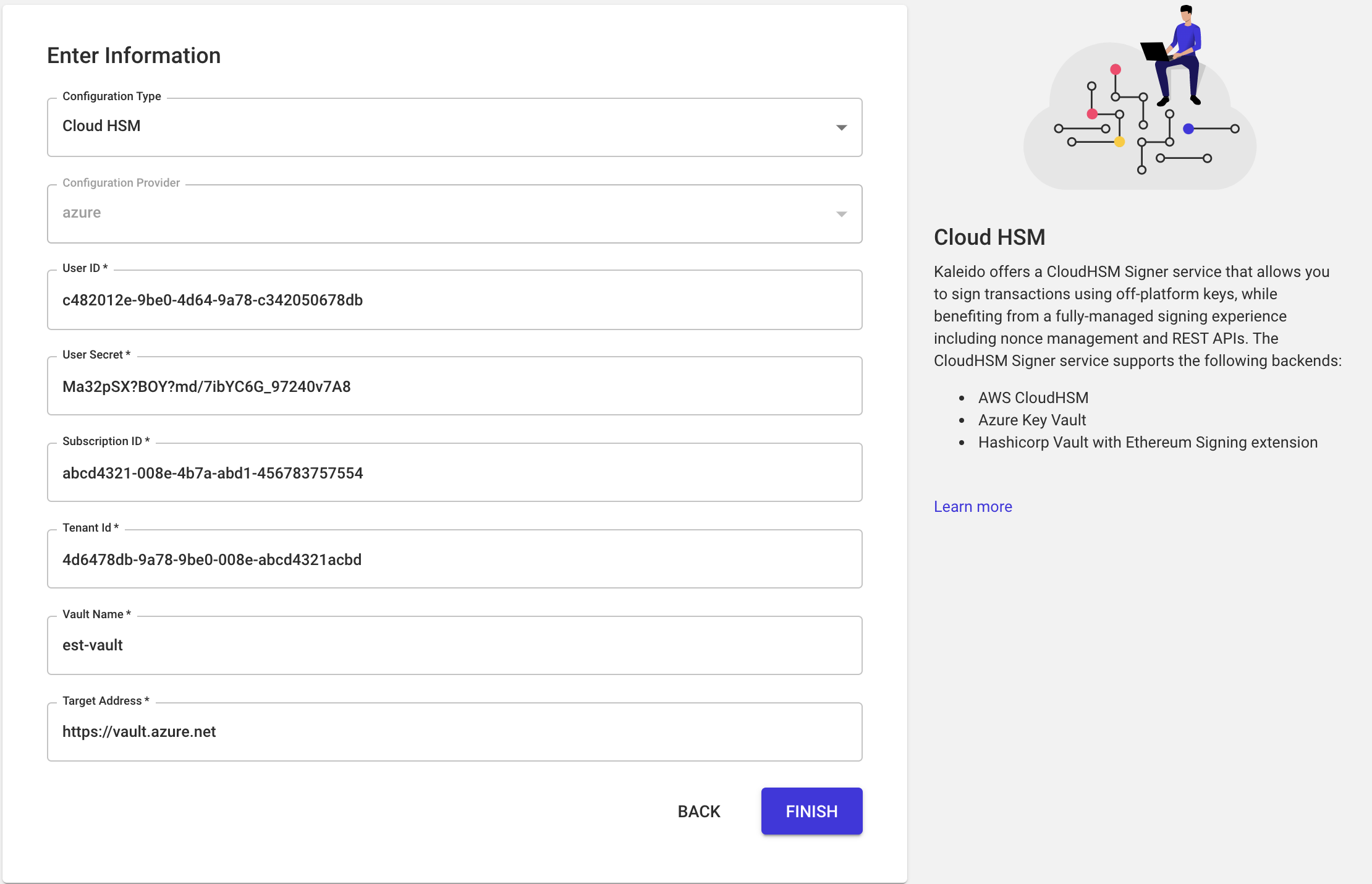
In your Kaleido environment, you need to create a Cloud Configuration of type Cloud HSM that provides connection/authentication parameters to reach your Cloud HSM backend. In your environment dashboard click on the following in the left-hand nav:
Manage Resources -> Cloud Configurations -> Cloud HSM
Pick the membership in which you would like to create the Cloud HSM configuration. The configuration will then be available to associate with any Cloud HSM Signer created in this environment, under the same membership.
The final step is to create a Cloud HSM Wallet that uses a Cloud HSM Configuration you created in the previous step. You will need to have at least one node in the same membership as the Cloud HSM Wallet you are about to create. The wallet is bound to the node for any access to the blockchain such as to submit transactions.
Once the wallet is active, you can sign transactions using the Cloud HSM Wallet by specifying the account address associated with a key that is stored in the Cloud HSM backend. The Cloud HSM Wallet will never be able to download private keys from the Cloud HSM backend. The wallet will generate signing requests to the Cloud HSM backend by specifying the address associated with the secp256k1 key.
In your environment dashboard click on the following in the left-hand nav:
Manage Resources -> Key Management -> Cloud HSM Wallets
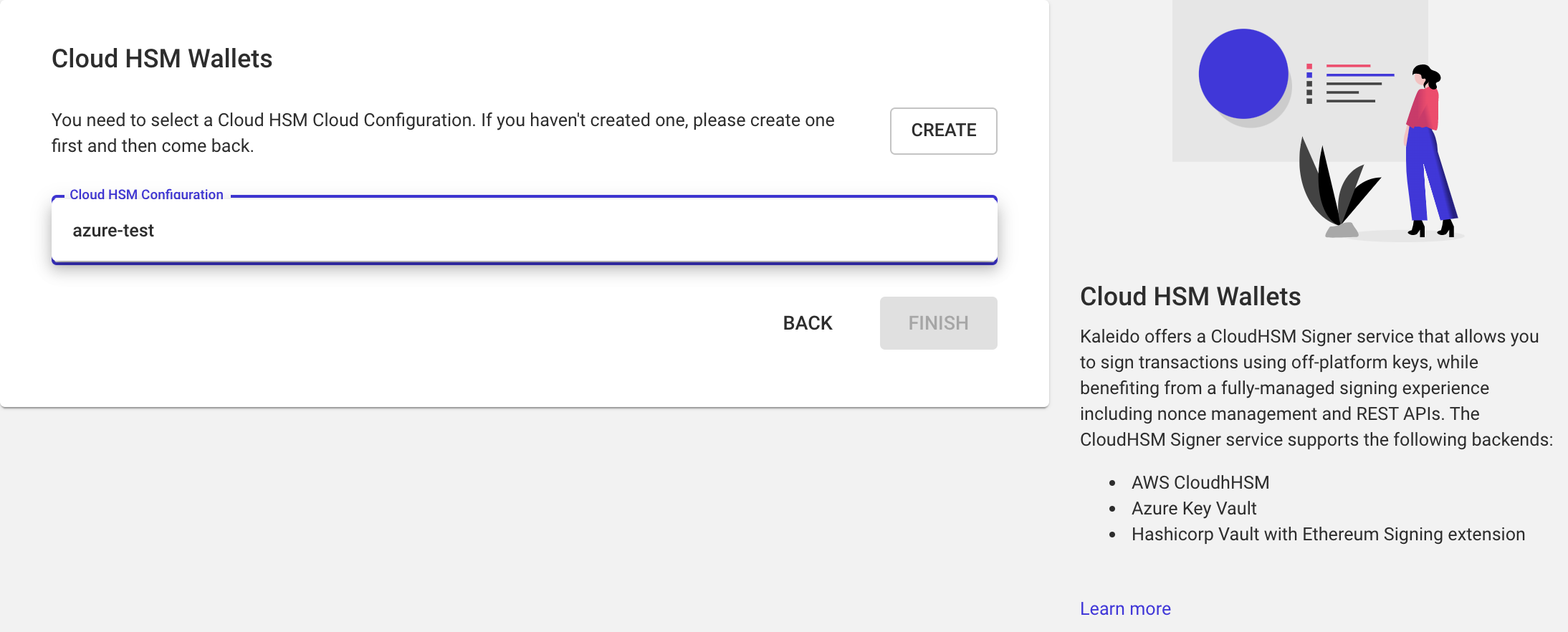
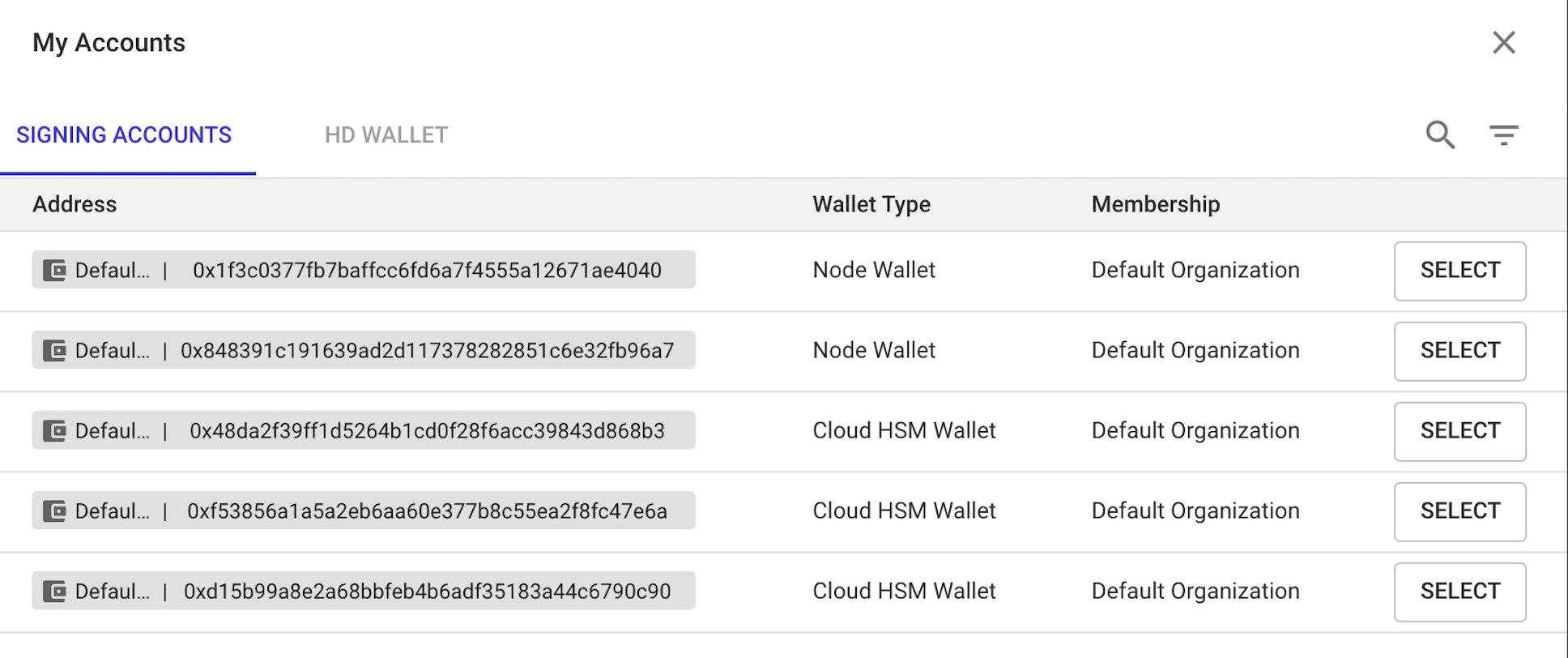
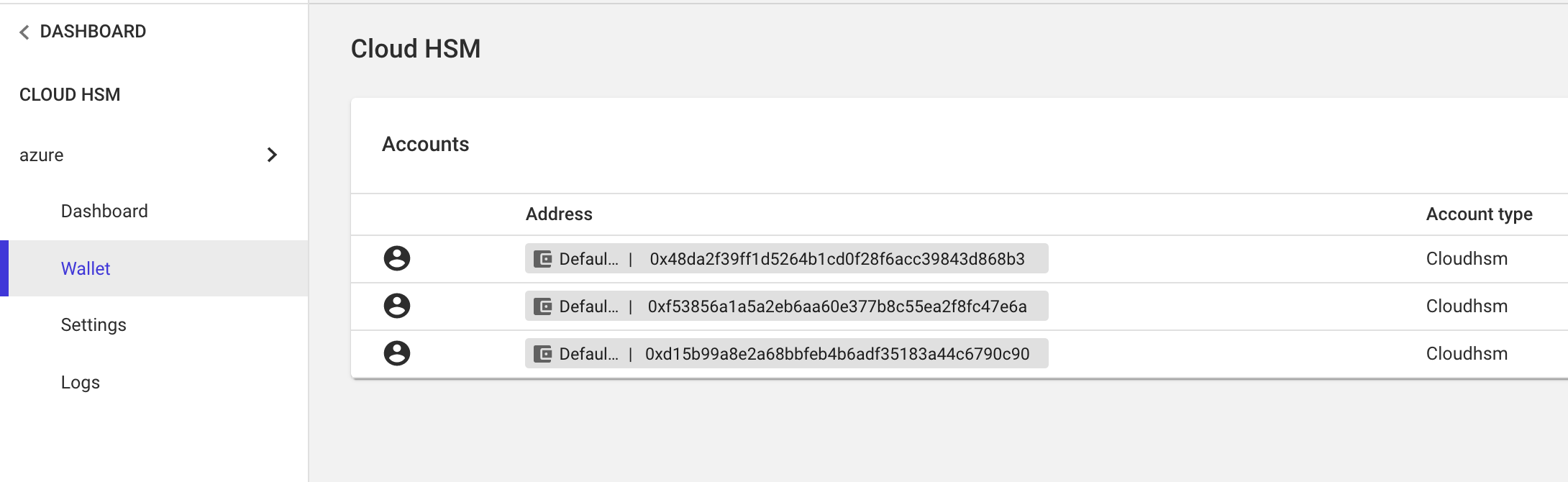
Select a Membership in which the Cloud HSM Wallet is to be created and select the Cloud HSM Configuration that should be used by the wallet. Once the wallet is created, it attempts to connect to the Cloud HSM backend and retrieves the list of account addresses with keys of type secp256k1, the Elliptic Curve type used in ethereum. To view account addresses, Click on View Wallet for the wallet you created and in the Cloud HSM dashboard, click on the following in the left nav:
Cloud HSM -> Wallet
If you added keys to the cloud HSM backend after the Cloud HSM Wallet was created, you need to click on Refresh Accounts button in this page to let the Cloud HSM Wallet query the updated account list from the backend
Transactions can be submitted directly to the Cloud HSM Wallet or by referencing one of the HSM stored addresses as a Signing Address when deploying contracts/submitting transactions in Gateway APIs and Tokens/Digital Assets workflows. When a transaction is received for signing by Cloud HSM wallet, the wallet:
Transactions can be submitted to the Cloud HSM Wallet’s RPC/WSS URLs (available via the service’s /status API) with a from address that is one of the addresses in the Wallet.
Use a Cloud HSM address in the kld-from field in the API request or the Swagger UI when submitting a transaction to a Gateway API. This will result in the transaction being signed using the key associated with the address.
When deploying Tokens, the UI provides an option to pick the Signing Account where the list of addresses from each Wallet is displayed. Pick an address from a Cloud HSM Wallet so that the Token deployment is signed by the key associated with an address in the Cloud HSM Wallet